Quantum Resilience: How Blockchain is Outpacing the Quantum Threat
As we enter the age of quantum computing, it’s crucial to acknowledge both the risks and benefits of this transformative technology—particularly how it might impact the blockchain technology underpinning cryptocurrencies and Bitcoin. The emergence of quantum computers capable of breaking current cryptographic standards represents a potential Gordian knot of security challenges for our digital economy.
This article explores how quantum computing works, examines potential threats to both traditional and blockchain-based financial systems, and highlights why blockchain networks may be better positioned to adapt to quantum threats through protocol upgrades and their decentralized architecture. For consumers and businesses concerned about digital security in the quantum era, understanding these distinctions is increasingly important for making informed decisions about financial technology.
Bottom Line Up Front (BLUF)
- Universal Quantum Threat: Quantum computing poses significant security risks to all digital systems, impacting both traditional financial infrastructures and blockchain networks. These emerging threats necessitate a comprehensive re-evaluation of current cryptographic protocols.
- Blockchain’s Intrinsic Advantages: Despite the universal risk, blockchain networks—exemplified by Bitcoin—offer built-in resilience through decentralized architecture. Their ability to implement protocol upgrades provides a strategic edge over centralized systems when adapting to quantum challenges.
- Contrasting System Vulnerabilities: Traditional electronic financial infrastructures, with their centralized security models and legacy systems, are particularly susceptible to quantum-enabled breaches. In contrast, blockchain’s distributed nature minimizes single points of failure, enhancing overall system robustness.
- Proactive Security Strategies: The article emphasizes the importance of transitioning to quantum-resistant algorithms and rigorous key management to fortify digital security. With proper preparation and continuous protocol improvements, blockchain networks are better positioned to withstand future quantum attacks.
The Integrity of Blockchain
Decentralization as a Security Feature
Blockchain technology provides an innovative approach to security through its decentralized architecture. Unlike traditional financial systems that rely on centralized security protocols, blockchain distributes trust across a vast network of nodes. According to a study by the National Institute of Standards and Technology (“NIST”), blockchain technology has the potential to provide new infrastructure to enhance the security of existing services [^1].
The Bitcoin network, specifically, represents the most secure blockchain implementation due to its extensive hash rate and distributed validator network. Bitcoin’s security model ensures integrity, reduces certain transaction costs compared to legacy financial institutions, and creates a highly resilient system. Thanks to its large network of decentralized nodes, the computing power and costs required to compromise the network and alter or create fraudulent transactions are prohibitively high.
Bitcoin’s Computational Fortress
For reference, the Bitcoin network now operates at an astonishing 864 exahashes per second—an enormous leap from roughly 300 exahashes per second in 2023—thanks to thousands of miners whose combined specialized hardware continually drives up the total hash rate; as a result, even if a single computer were to attempt 3×10^20 hash calculations, it would take approximately 9.5 million years to complete, making any attack on the blockchain a pyrrhic victory even for a network of supercomputers.[^2]
This security does not mean blockchain is invulnerable. Key risks to Bitcoin include 51% attacks (where a single entity controls the majority of mining power), poor wallet security practices, and vulnerabilities in exchange platforms. However, the Bitcoin development community has demonstrated the ability to implement protocol upgrades to address emerging security challenges—a critical capability when confronting quantum threats.
The Gordian Knot
In essence, blockchain functions as a sort of modern-day Gordian Knot. In antiquity, the Gordian Knot was a series of incredibly complicated knots so intertwined that it was impossible to see how they were all fastened [^3]. The knot was fastened to an ox cart belonging to founder King Gordias of Phrygia.

The knot’s significance came from a prophecy: whoever untangled this wicked web would become ruler of all Asia. Alexander the Great, upon encountering the knot, initially attempted to unfasten it through conventional means. When that failed, he drew his sword and cut the knot in half, thus freeing the cart and fulfilling the prophecy[^4].
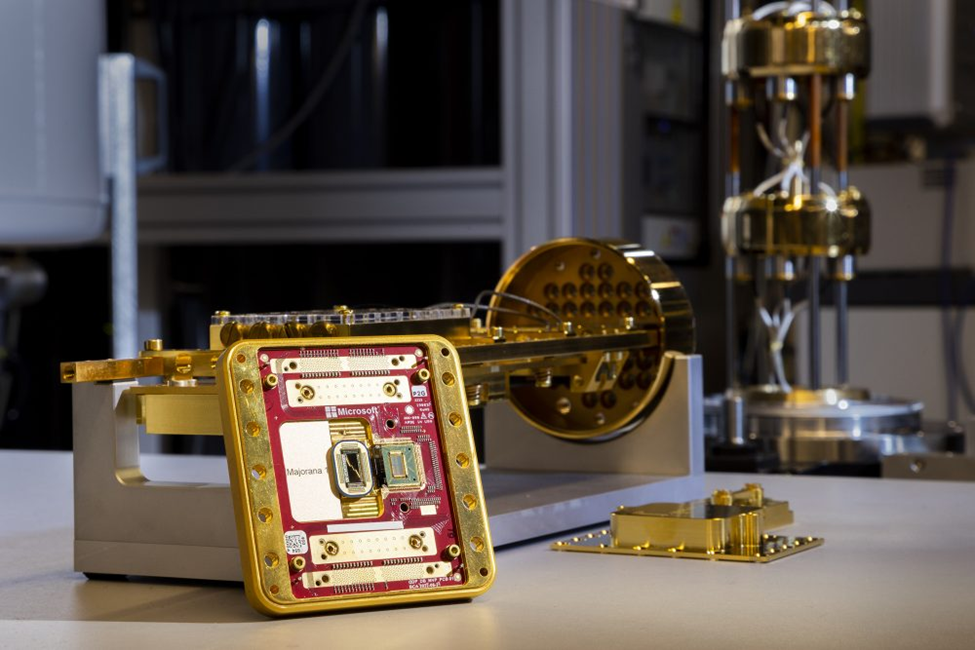
At present time, quantum computing represents a potential “Alexander’s sword” that could cut through current cryptographic protections. In December 2024, Google unveiled their latest quantum chip called Willow[^5], and in February 2025, Microsoft introduced their Majorana 1 chip[^6]. These developments signal the accelerating pace of quantum computing advancement.
However, unlike the Gordian Knot, blockchain technology can adapt. Where Alexander’s opponents could only watch as their knot was severed, blockchain networks can implement quantum-resistant cryptographic standards to maintain security. This adaptability represents a crucial advantage over many traditional systems.
Quantum Computing Basics: A Marine Grunt’s Perspective
What is Quantum Computing?
Quantum computing’s power comes from its ability to perform calculations in more than one logical state simultaneously. To understand this concept, we should first consider how traditional computing works.
A traditional computer, like your smartphone, performs operations via logic gates (think simple arithmetic: 2 + 2 = 4 is a TRUE statement, while 2 + 2 = 5 is FALSE). An output value of TRUE would be represented by a 1, while FALSE is represented by a 0. This 0 or 1 state is known as a bit, and it operates in a binary fashion.
Modern computers perform billions of these bit operations per second. However, as the amount of data and operations required for higher-level tasks increases, so do the computational resource requirements. When applied to something like blockchain, where millions of computers are performing complex hash functions (cryptographic algorithms that convert input data into fixed-length outputs serving as digital fingerprints; SHA 256), the distributed nature becomes very resource-intensive and costly for any single entity to undermine (pun intended); the current strength of blockchain in a classical computing environment.
The Quantum Difference: Qubits and Superposition
Quantum computing fundamentally changes this paradigm. Instead of using bits with a single 0 or 1 state, quantum computers use qubits (quantum bits) which can represent multiple states simultaneously. While a classical bit can only be 0 or 1, a qubit can exist in a superposition of both states.
The concept of superposition is what gives quantum computers their extraordinary power. Superposition allows multiple states to exist simultaneously until an operation is performed and the qubit is measured. This ability to process multiple potential outcomes at once is what makes quantum computing exponentially more powerful than classical computing for certain types of problems.
Chuck E. Cheese Ski Ball Tickets and Prize Preference Determination
To illustrate, consider a child trying to decide which prize to buy with their tickets at Chuck E. Cheese. In a classical computing approach, if the child (let’s call him Jesse) has earned enough tickets for one toy, he would:
- Make a decision (perform an operation)
- Choose a toy (Toy A)
- Play with the toy to determine how much utility/joy it delivers
- If he wants to try another toy, he would need to start the process over—earn more tickets, select a different toy (Toy B), play with it, and then compare which toy (A or B) was more enjoyable
The only truly determinative way to find the optimal toy would be to repeat this entire process for every possible option—inefficient and time-consuming.

A quantum computer approaches this problem differently. Instead of sequential iterations, qubits allow a system to evaluate multiple potential outcomes simultaneously. In our analogy, quantum computing would allow Jesse to essentially “see” how much fun he would have with each toy simultaneously. Because qubits can exist in superposition, they can represent multiple possible values until measured.
This capability becomes exponentially more powerful when scaled. The computational advantage grows dramatically with each additional qubit, just as the efficiency advantage would grow if we applied this quantum approach to every child visiting Chuck E. Cheese in a day.
Current Quantum Computing Power
Google’s Willow and Microsoft’s Majorana 1 quantum processors represent significant advances in quantum computing technology. Willow has the capability to process calculations using up to 100 qubits, which provides computational power that theoretically exceeds all the world’s supercomputers combined for certain specialized problems[^7].
This exponential leap in computational capability is what makes quantum computing both exciting and concerning for cryptographic security. In this sense, quantum computers truly represent a potential “sword” capable of cutting through current cryptographic protocols, including those used in blockchain networks.
Quantum Threats to Financial Systems
Risks to Traditional Financial Infrastructure
Traditional electronic financial systems face significant vulnerabilities in a post-quantum world. These systems typically rely on centralized security architectures with numerous potential points of failure:
- Legacy System Vulnerabilities: Many financial institutions operate on outdated systems that would be challenging to upgrade comprehensively for quantum resistance.
- Centralized Attack Surface: Traditional financial networks have concentrated points of vulnerability that, once breached, could compromise entire systems.
- Complex Upgrade Paths: The fragmented nature of global financial infrastructure means implementing quantum-resistant protocols would require coordinated action across thousands of independent organizations.
The U.S. Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency (“CISA”) has identified financial services as a critical infrastructure sector potentially vulnerable to quantum attacks, noting that organizations that fail to prepare for the transition to post-quantum cryptography risk devastating consequences [^8].
Specific Risks to Blockchain Networks
While blockchain networks possess certain security advantages, they are not immune to quantum threats:
- Legacy Wallet Vulnerability: A major concern in a post-quantum world is the large number of legacy crypto wallets that are either inaccessible or infrequently utilized. If quantum computers can derive private keys from public addresses, these wallets could be compromised without the owner’s knowledge.
- Cold Storage Misconceptions: Even offline cold storage solutions remain vulnerable if their public keys have been exposed. As noted by quantum security company Qrypt, “although offline, if the wallet public key is found, it would be sufficient to calculate the private key and thus gain access to the stored crypto”[^9].
- Market Confidence Issues: Beyond direct security breaches, losing confidence in underlying cryptographic stability could lead to falling prices and investor selloffs, potentially slowing blockchain adoption across various sectors.
- National Security Implications: Quantum vulnerabilities could affect proposed governmental blockchain initiatives like strategic Bitcoin reserves, potentially undermining national security efforts as advanced persistent threats like state-sponsored actors might attempt to transfer these assets.
- Unknown Vulnerabilities: Perhaps most concerning are the undiscovered, “unknown unknowns” vulnerabilities that might only become apparent once quantum computing reaches certain capability thresholds.
Why Blockchain May Better Weather the Quantum Storm
Despite these risks, blockchain networks possess several key advantages that may make them more resilient to quantum threats than traditional systems:
Protocol Upgrade Capability
Blockchain networks have demonstrated the ability to implement significant protocol changes through software upgrades and forks. This flexibility allows for implementing quantum-resistant cryptographic algorithms across the entire network, quickly and efficiently. The Bitcoin community has previously coordinated significant upgrades, such as SegWit and Taproot, demonstrating the feasibility of such changes.
NIST has been working to develop quantum-resistant cryptographic standards, noting that blockchain systems have shown they can evolve to incorporate new capabilities through socially negotiated upgrades[^10].
Distributed Security Model
Blockchain’s decentralized architecture means that attackers would need to compromise many nodes simultaneously rather than a single point of failure. This distributed security model creates inherent resilience against attacks, even quantum-based ones.
Economic Disincentives
The economic structure of blockchain networks like Bitcoin creates disincentives for attacks. Even with quantum capabilities, an attacker who successfully compromised the network would likely devalue the very assets they aimed to steal, limiting the economic rationality of such attacks.
Community Vigilance
The open-source nature of many blockchain projects creates a global community of security researchers actively monitoring for vulnerabilities. This collective vigilance increases the likelihood of early detection and mitigation of quantum threats.
Time Advantage
Most experts believe that practical quantum computers capable of breaking current cryptographic standards are still years away from deployment. This timeline provides blockchain developers with a window to implement quantum-resistant solutions before significant threats materialize.
As the Defense Advanced Research Projects Agency (“DARPA”) has noted, the transition to post-quantum cryptography is as much about preparation and process as it is about the technology itself [^11].
The Path Forward: Quantum Resilience Strategies
For Blockchain Networks
Several approaches can enhance blockchain’s quantum resilience:
- Quantum-Resistant Algorithms: Implementing new hash algorithms that are computationally intensive even for quantum computers. NIST’s post-quantum cryptography standardization project has identified several promising candidates [^14].
- Protocol Forks: Creating forks between old and new cryptographic standards to maintain backward compatibility while enhancing security.
- Address Reuse Prevention: Discouraging the reuse of blockchain addresses, as quantum vulnerabilities increase with address exposure.
- Signature Scheme Upgrades: Transitioning from current digital signature schemes to quantum-resistant alternatives.
For Consumers and Investors
Individual users can also take steps to enhance their security:
- Security-First Storage: Utilizing institutional-grade storage solutions that implement rigorous security features and insurance protection.
- Regular Transfers: Moving assets to new addresses that utilize the most current cryptographic standards.
- Portfolio Diversification: Considering investment in protocols that are actively developing post-quantum security measures.
- Security Awareness: Maintaining vigilance about personal security practices, including proper key management and avoiding sharing sensitive information.
CHPG’s Quantum-Ready Blueprint: Institutional-Grade Storage, Insurance, and Blockchain Resilience
The emergence of practical quantum computing represents both a challenge and an opportunity for digital financial systems. While no system—traditional or blockchain-based—is completely immune to quantum threats, blockchain networks possess key architectural advantages that may allow them to better adapt to these challenges. CHPG is proactively preparing for a quantum future by leveraging institutional-grade storage and insurance to safeguard digital assets. This dual approach not only protects holdings from physical and cyber threats but also provides a robust foundation for integrating emerging quantum-resistant technologies.
The decentralized nature of blockchain, combined with its demonstrated ability to implement protocol-wide upgrades, creates a resilience that many centralized systems lack. For consumers and businesses concerned about long-term digital security, understanding these distinctions is increasingly important for making informed financial technology decisions.
As we progress into the quantum era, continued vigilance, research, and protocol improvements will be essential to maintaining the security and integrity of all digital financial systems. The technological Gordian Knot presented by quantum computing may not be entirely avoidable, but with proper preparation—such as that employed by CHPG—blockchain networks may have the best chance of preserving their security in this new paradigm.
Sources
[^1] D. Yaga et al., Blockchain Technology Overview, NISTIR 8202 (2019).
[^2] See CoinWarz Bitcoin Hashrate Chart, available at https://www.coinwarz.com/mining/bitcoin/hashrate-chart.
[^3] E. Andrews, What Was the Gordian Knot?, History.com (Aug. 22, 2016), https://www.history.com/news/what-was-the-gordian-knot.
[^4] Digital Gordion | The Gordian Knot, University of Pennsylvania Museum of Archaeology and Anthropology (n.d.), available at https://www.penn.museum/sites/gordion/articles/myth-religion/the-gordian-knot/.
[^5] H. Neven, Introducing Willow: Google’s Next Generation Quantum Processor, Google AI Blog (Dec. 9, 2024), available at https://blog.google/technology/research/google-willow-quantum-chip/.
[^6] M. Bolgar, Microsoft Unveils Majorana 1: A Quantum Leap Forward, Microsoft Research Blog (Feb. 19, 2025), available at https://news.microsoft.com/source/features/innovation/microsofts-majorana-1-chip-carves-new-path-for-quantum-computing/.
[^7] T. Greene, Google’s New “Bristlecone” Chip Could Make Quantum Computers Actually Useful, The Next Web (Mar. 6, 2018), available at https://thenextweb.com/news/google-reclaims-quantum-computer-crown-with-72-qubit-processor/.
[^8] Cybersecurity and Infrastructure Security Agency, Post-Quantum Cryptography (2022), available at https://www.dhs.gov/quantum.
[^9] Qrypt, Quantum Threats to Blockchain Technologies (2023), available at https://www.qrypt.com/resources/risk-of-quantum-computing-crypto-wallets/.
[^10] Post-Quantum Cryptography Standardization, National Institute of Standards and Technology, available at https://csrc.nist.gov/projects/post-quantum-cryptography/post-quantum-cryptography-standardization.
[^11] DARPA, Quantum Computing Prototype (2024), available at https://www.darpa.mil/news/2024/quantum-computing-prototype.
[^12] NIST Releases First 3 Finalized Post-Quantum Encryption Standards, National Institute of Standards and Technology (2024), available at https://www.nist.gov/news-events/news/2024/08/nist-releases-first-3-finalized-post-quantum-encryption-standards.